AutoPhish vs RocketShare
Side-by-side comparison to help you choose the right product.
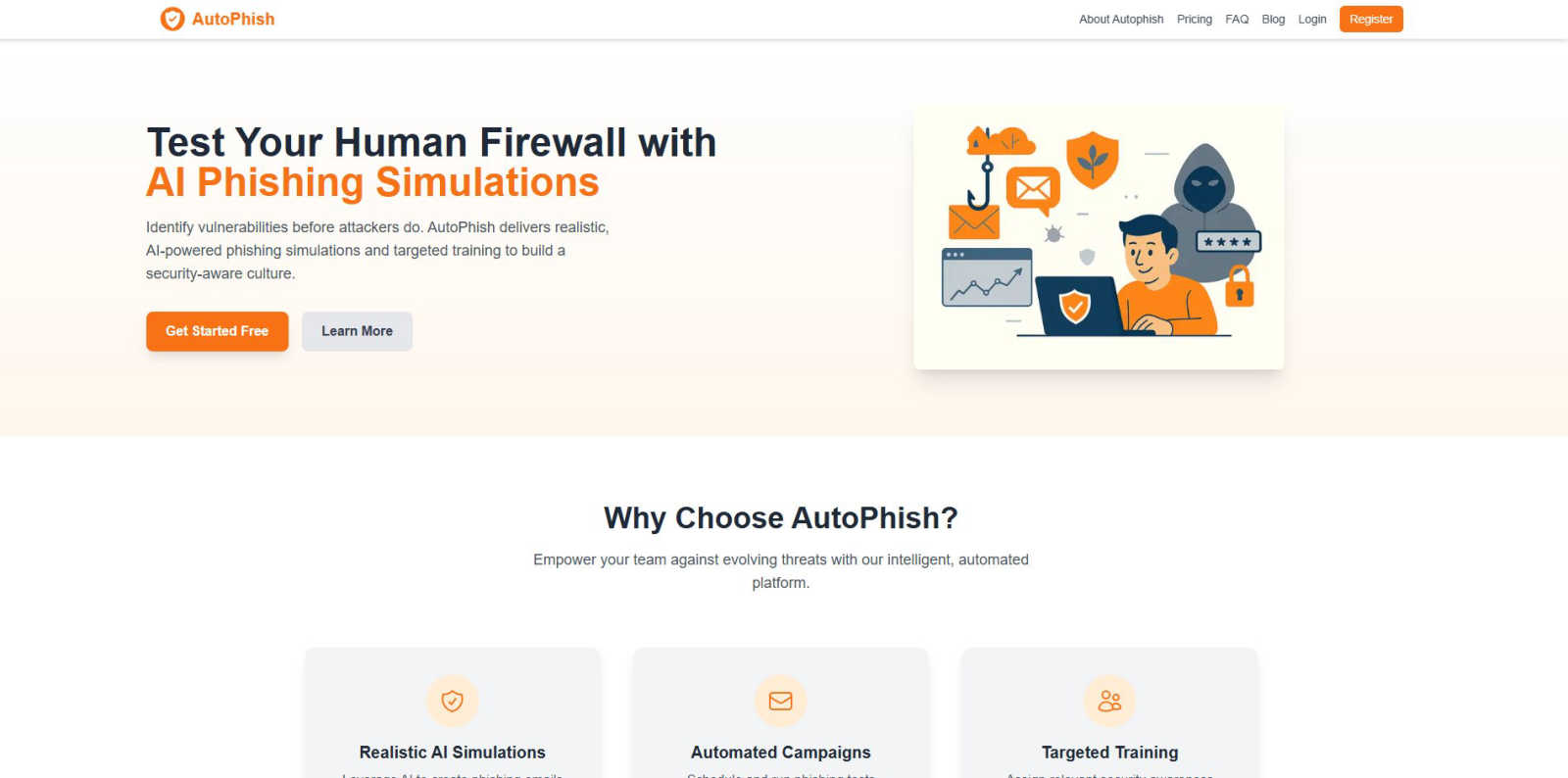
AutoPhish automates phishing simulations and tailored training to enhance your team's security awareness and resilience.
Last updated: March 1, 2026
RocketShare
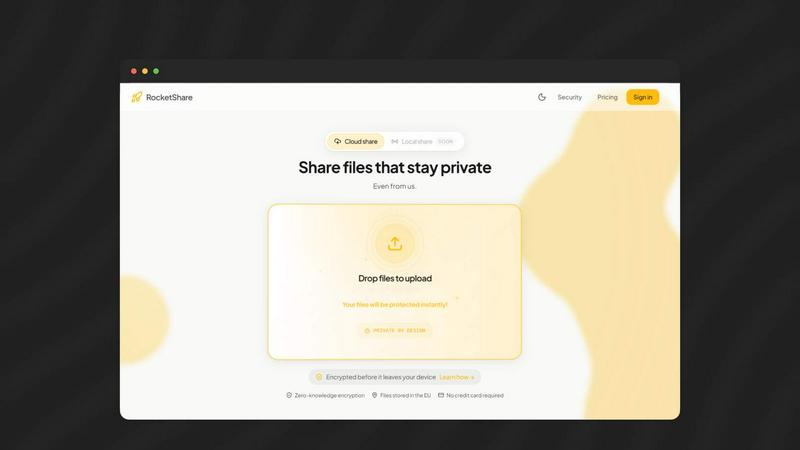
RocketShare provides secure, private file sharing with client-side encryption that even its operators cannot access.
Last updated: March 4, 2026
Visual Comparison
AutoPhish
RocketShare
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish leverages advanced AI technology to create highly realistic phishing emails that mimic actual cyber threats. This feature ensures that simulations are not only relevant but also designed to test employees' ability to recognize and respond to potential phishing attacks specific to their industry.
Automated Campaigns
With AutoPhish, organizations can schedule and run phishing tests automatically, which streamlines the process of conducting regular security assessments. This feature saves time and ensures consistent training, allowing companies to focus on other critical aspects of their cybersecurity strategy.
Targeted Training
AutoPhish provides targeted security awareness training based on the results of phishing simulations. By analyzing user performance, the platform assigns relevant training modules to individuals based on their specific vulnerabilities and roles within the organization, enhancing the effectiveness of the training.
Comprehensive Analytics
The platform offers advanced reporting and analytics capabilities, allowing organizations to monitor results in real time. This feature helps identify vulnerable users, track improvement over time, and assess the overall effectiveness of the phishing simulation campaigns and training programs.
About RocketShare
Zero-Knowledge End-to-End Encryption
This is the cornerstone feature of RocketShare. File encryption occurs locally on the user's device before upload, using a unique key that is never transmitted to or stored on RocketShare's servers. The platform has zero knowledge of the file contents or the password protecting the transfer. This architecture guarantees that only the intended recipient, who possesses the correct key (typically within the share link), can decrypt and access the files, providing absolute confidentiality against external threats and internal access.
Dual Sharing Modes: Cloud and Local (P2P)
RocketShare offers flexible transfer methods to suit different security and speed requirements. The Cloud Share option uploads encrypted files to secure EU-based servers for asynchronous sharing, ideal for sending large files without requiring the recipient to be online simultaneously. The Local Share (peer-to-peer) mode establishes a direct, encrypted connection between devices for transfer, with files never touching any intermediary server. This provides maximum speed and reduces the data's digital footprint, perfect for highly sensitive transfers on a local network.
Privacy-First Data Handling and Storage
All data processed through RocketShare's cloud service is stored exclusively on servers located within the European Union, ensuring compliance with robust data protection regulations like the GDPR. The platform's design ensures that even stored data remains in its encrypted state, inaccessible to the hosting provider. This commitment extends to operational practices, including a transparent privacy policy and a clear data handling framework that prioritizes user sovereignty over their information.
Simple, Self-Serve User Interface
Despite its powerful security underpinnings, RocketShare presents a minimalist and intuitive user experience. The core functionality revolves around a straightforward drag-and-drop or click-to-browse upload interface. The complexity of encryption is handled seamlessly in the background, allowing users to send files securely without needing technical expertise. This design philosophy makes enterprise-level security accessible to freelancers, small teams, and large organizations alike.
Use Cases
AutoPhish
Enhancing Employee Awareness
Organizations can use AutoPhish to conduct phishing simulations that help employees recognize and respond to phishing attempts. By experiencing realistic scenarios, employees become more vigilant and aware of potential threats, reducing the likelihood of successful attacks.
Assessing Cybersecurity Posture
IT departments can utilize AutoPhish to regularly assess their organization’s cybersecurity posture. By analyzing simulation results, they can identify weaknesses within the team and implement training strategies to address these vulnerabilities effectively.
Compliance and Regulatory Training
Companies in regulated industries can leverage AutoPhish to ensure compliance with cybersecurity training requirements. The platform can provide documented proof of training sessions and assessments, which is crucial for meeting industry standards and regulatory mandates.
Incident Response Preparation
Using AutoPhish, organizations can prepare their teams for potential phishing incidents by simulating various attack scenarios. This proactive approach ensures that employees are not only aware of the threats but also equipped with the knowledge and skills to respond effectively, minimizing impact in the event of a real attack.
RocketShare
Legal Document and Case File Exchange
Law firms and legal professionals routinely handle highly confidential case files, client communications, and evidentiary materials. RocketShare ensures these documents are protected by unbreakable encryption from the moment they leave the sender's computer. The zero-knowledge model guarantees attorney-client privilege is technically upheld, as not even the file-sharing provider can access the content, making it an ideal tool for secure collaboration between legal teams, clients, and external counsel.
Healthcare Data and Patient Record Sharing
Healthcare providers, clinics, and researchers need to share sensitive patient records, lab results, and medical imaging while strictly complying with regulations like HIPAA. RocketShare's end-to-end encryption and EU data storage provide a secure conduit for such information. By ensuring data is encrypted before transit and remains encrypted at rest, it significantly mitigates the risk of data breaches and unauthorized access during digital transfer.
Creative Asset Delivery for Photographers and Videographers
Photographers and videographers can deliver high-resolution client galleries, raw footage, and final edits without fear of intellectual property theft or unauthorized distribution. RocketShare allows them to send files of any size securely, with the confidence that their creative work is protected throughout the transfer process. The platform's simplicity also enhances the client experience, providing a secure, professional delivery method compared to unencrypted email attachments or public cloud links.
Confidential Corporate Project Collaboration
Marketing agencies, game studios, and internal teams working on confidential projects—such as merger documents, unreleased product designs, or proprietary source code—require a secure collaboration channel. RocketShare facilitates the safe exchange of large project files between team members and external partners. The local P2P sharing option is particularly valuable for transferring massive files like 4K video projects or game builds within an office network at high speed, without exposing data to the wider internet.
Overview
About AutoPhish
AutoPhish is an innovative AI-powered platform designed to enhance organizational cybersecurity through realistic phishing simulations and targeted security awareness training. It serves as a proactive tool for businesses aiming to identify and mitigate vulnerabilities before cyber attackers can exploit them. The platform utilizes cutting-edge artificial intelligence technology to generate phishing emails that closely resemble real-world threats, ensuring that the simulations are relevant and tailored to the unique challenges faced by various industries. AutoPhish is suitable for organizations of all sizes, from small businesses to large enterprises, and emphasizes the importance of cultivating a culture of security awareness among employees. Its primary value proposition lies in its ability to empower teams with knowledge and skills to recognize and respond to phishing attempts effectively. By combining automated campaign management with personalized training modules, AutoPhish not only saves time and reduces costs but also enhances the overall security posture of organizations. Ultimately, the platform aims to create a robust defense against evolving cyber threats, ensuring that employees are well-equipped to protect sensitive information and organizational assets.
About RocketShare
RocketShare is a secure file-sharing platform architected from the ground up with an uncompromising commitment to user privacy. It operates on a foundational principle of zero-knowledge encryption, ensuring that files are encrypted on the sender's device before any data is transmitted. This means the encryption keys are never shared with RocketShare's servers; they remain solely with the user, often embedded directly within the shareable link. Consequently, the platform's infrastructure only ever handles cryptographically sealed, unreadable data, making it technically impossible for the service provider or any third party to access the file contents. This model delivers enterprise-grade security through a simple, self-serve interface, eliminating the complexity typically associated with high-level data protection. RocketShare caters to individuals, professionals, and businesses across various sectors who handle sensitive information, including legal documents, healthcare records, creative intellectual property, and confidential corporate data. Its core value proposition is providing top-tier, auditable security without sacrificing usability, offering both cloud-based transfers and local peer-to-peer sharing options. All cloud-stored data is housed within European Union data centers, adhering to strict regional data protection standards, making it a trusted solution for privacy-conscious users globally.
Frequently Asked Questions
AutoPhish FAQ
What industries can benefit from AutoPhish?
AutoPhish is designed to cater to a wide range of industries, including finance, healthcare, education, and technology. Any organization looking to enhance its cybersecurity awareness and training can benefit from the platform's tailored phishing simulations and training programs.
How does AutoPhish ensure realistic simulations?
AutoPhish uses advanced AI algorithms to analyze current phishing trends and craft simulations that closely mimic real-world threats. This includes customizing emails that reflect specific industry challenges, ensuring that simulations are relevant and effective in training employees.
Can I track the progress of my employees?
Yes, AutoPhish provides comprehensive analytics and reporting features that allow organizations to track employee performance during phishing simulations and training sessions. This helps identify strengths and weaknesses, enabling targeted follow-up training as needed.
Is there a free trial available for AutoPhish?
AutoPhish offers a free plan that allows organizations to start with basic phishing simulations and training. This enables potential users to evaluate the platform's effectiveness before committing to a paid plan, making it accessible for organizations of all sizes.
RocketShare FAQ
How does RocketShare's "zero-knowledge" encryption work?
Zero-knowledge encryption means RocketShare has no knowledge of or access to your files or their encryption keys. When you upload a file, it is first encrypted on your own device using a strong, unique key. This encrypted data is then sent to RocketShare's servers. The decryption key is not sent with the data; it is typically included in the shareable link you send to the recipient. Since the servers only ever receive and store the encrypted (scrambled) data, and RocketShare does not possess the key, it is technically impossible for anyone at the company to view your files.
Where are my files stored with RocketShare?
For files shared via the Cloud Share option, the encrypted data is stored on secure servers located within the European Union. This ensures that data residency complies with the EU's stringent General Data Protection Regulation (GDPR) framework. It is critical to understand that the files stored are in their encrypted state only. For files shared via the Local Share (peer-to-peer) mode, the data never touches any external server; it is transferred directly between the devices involved in the transfer.
Is there a file size limit for transfers?
Based on the provided context, RocketShare is designed to allow users to send "files of any size." This indicates that the platform does not impose restrictive file size limits commonly found in email or other basic file-sharing services. This makes it exceptionally suitable for transferring very large files, such as high-resolution video projects, extensive datasets, or comprehensive design packages, without requiring compression or splitting into multiple parts.
Do I need to create an account or provide payment details to use RocketShare?
No, you can use RocketShare's core file-sharing functionality without creating an account or providing a credit card. The platform emphasizes a self-serve, privacy-first model where you can start sharing files immediately. This approach lowers the barrier to entry and aligns with the privacy ethos by minimizing the collection of personal data. Account creation may be optional for accessing additional features or management tools, but it is not a prerequisite for sending secure files.
Alternatives
AutoPhish Alternatives
AutoPhish is an advanced AI-powered platform designed to enhance cybersecurity by providing automated phishing simulations and tailored security awareness training. As part of the cybersecurity training category, it focuses on empowering organizations to identify and mitigate vulnerabilities before they can be exploited by cyber attackers. Users often seek alternatives to AutoPhish for various reasons, including pricing considerations, specific feature sets, or compatibility with existing platforms and workflows. When choosing an alternative, it is essential to evaluate the effectiveness of the phishing simulations, the quality of training materials, and the overall ease of integration with current security practices within the organization. When exploring alternatives, organizations should prioritize features that enhance user engagement, provide comprehensive reporting and analytics, and allow for customization based on industry-specific threats. Additionally, it's crucial to consider the scalability of the platform, ensuring it can adapt to the growing needs of the organization as it evolves. By focusing on these key aspects, businesses can find a solution that not only meets their immediate needs but also fosters a long-term culture of security awareness.
RocketShare Alternatives
RocketShare is a secure file-sharing platform in the Productivity & Management category, distinguished by its zero-knowledge encryption model. This ensures that files are encrypted on the user's device before upload, making the content inaccessible to anyone, including the service provider itself. Users may seek alternatives to RocketShare for various reasons, such as differing budget constraints, the need for specific collaboration features like real-time editing or team workspaces, or a preference for different storage locations and data residency laws. Platform compatibility, such as the need for a dedicated mobile app or integration with existing software ecosystems, is another common driver for exploring other options. When evaluating an alternative, key considerations should include the provider's security model and privacy policy, especially regarding encryption and data access. It is also crucial to assess file size limits, transfer speeds, storage duration policies, and the overall user experience. The ideal service balances robust security with the practical features required for your specific use case, whether for individual, business, or collaborative needs.

