iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
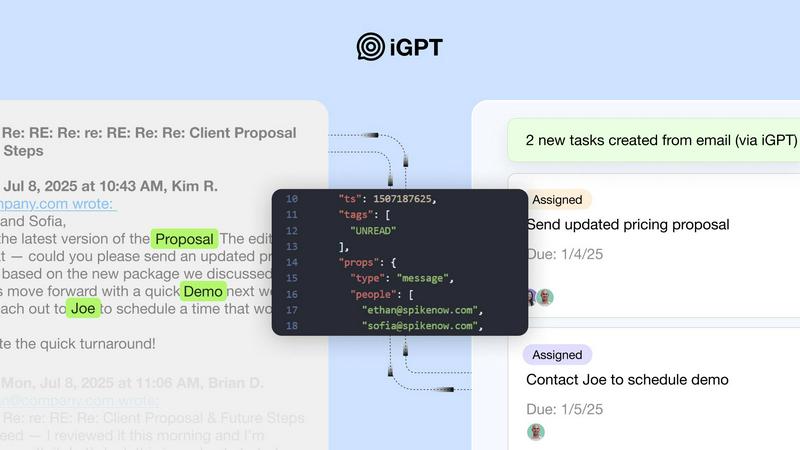
iGPT is an enterprise API that transforms email data into context-aware, actionable insights for AI agents and.
Last updated: February 28, 2026
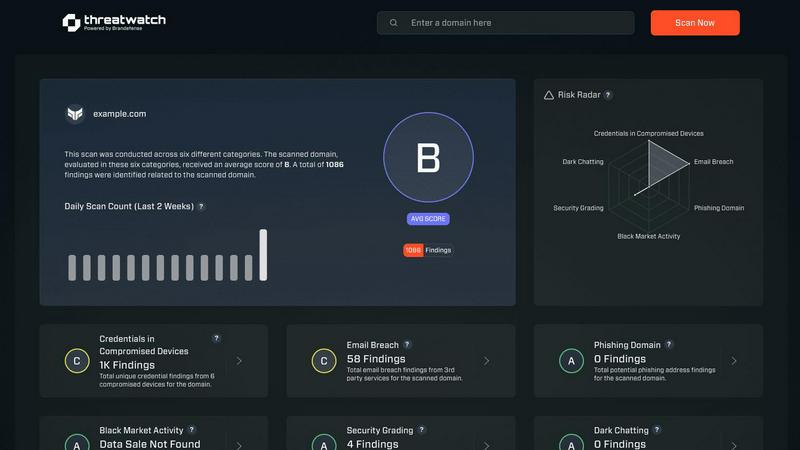
Threat Watch
Threat Watch swiftly evaluates your cybersecurity health by identifying vulnerabilities in compromised accounts and.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
iGPT consolidates the entire complexity of email intelligence into a single, natural language API call. This unified endpoint seamlessly handles retrieval, context shaping, and reasoning in one integrated pipeline, eliminating the need for developers to manage separate systems for parsing, vector stores, or complex prompt chains. Users simply send a query, and the API returns a structured, contextual answer with citations, dramatically reducing development time and maintenance overhead for building email-aware applications.
Advanced Context Engineering Framework (CEF)
The platform employs a sophisticated Context Engineering Framework that automatically optimizes how information is retrieved and presented to large language models. It performs hybrid retrieval combining semantic, keyword, and filter-based searches, which are then intelligently scored and reranked. The framework also automatically reconstructs full email threads across time and participants, shapes the optimal context window for the LLM, and ensures every piece of information in the response is traceable back to its source email or attachment.
Enterprise-Grade Security & Compliance
iGPT is built with a foundational commitment to data security and privacy. It operates on a zero-data training and zero-data retention policy, ensuring customer data is never used to train models or stored post-processing. It supports OAuth-only authentication with strict Role-Based Access Control (RBAC) and provides comprehensive audit trails. This architecture guarantees that sensitive email communications remain under the company's control, making it suitable for highly regulated industries like finance, legal, and healthcare.
Real-Time Ingestion & Attachment Processing
The system continuously and instantly indexes new email messages and attachments as they arrive, ensuring that the intelligence provided is always based on the most current data. Its powerful attachment processing engine deeply extracts text, data, and structural information from a wide array of file formats, including documents, PDFs, and spreadsheets. This allows iGPT to understand and reason over the complete content of an email thread, not just the body text, unlocking insights buried in complex documents.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch offers a holistic evaluation of an organization's cybersecurity landscape. This feature analyzes critical security categories, providing users with a detailed understanding of their cyber health and highlighting vulnerabilities that need immediate attention.
Real-Time Insights and Alerts
With its real-time monitoring capabilities, Threat Watch continuously scans for potential threats and vulnerabilities. Users receive instant alerts when issues arise, allowing them to respond quickly and effectively to mitigate risks before they escalate.
Dark Web Monitoring
One of the standout features of Threat Watch is its ability to monitor the dark web for compromised credentials and sensitive information. This proactive approach helps organizations stay ahead of potential threats and protects their valuable data from being exploited by malicious actors.
Automated Risk Assessments
Threat Watch automates the process of risk assessment, enabling organizations to quickly identify and prioritize potential vulnerabilities. This efficiency not only saves time but also ensures that security teams can focus their efforts on the most critical issues affecting their cybersecurity posture.
Use Cases
iGPT
Intelligent Email Assistants & Copilots
Developers can build sophisticated AI agents that draft, prioritize, summarize, and act on email with full historical and contextual understanding. These assistants can manage inboxes, flag urgent items, suggest replies based on past correspondence, and automate routine communication tasks, significantly boosting productivity for individuals and teams who rely heavily on email for daily operations.
Automated Workflow & Project Management
iGPT can automatically transform email threads into structured tasks, deadlines, approvals, and calendar events. By analyzing conversation threads and attachments, it can identify action items, assign owners, track project momentum, and flag stalled discussions or missed deadlines, seamlessly bridging communication data with project management tools and CRMs.
Customer Support & Relationship Management
Support copilots powered by iGPT can rebuild the complete customer story by analyzing long, complex email chains, tone shifts, and all related attachments. This provides support agents with immediate, full-context understanding of a customer's issue history. For sales teams, CRM agents can extract deal decisions, ownership changes, and key discussion points directly from email threads to keep CRM records accurate and actionable.
Compliance Auditing & Legal Discovery
In regulated environments, iGPT serves as a powerful tool for compliance and legal e-discovery. It can trace feedback, approvals, contractual terms, and decision-making rationale directly back to the original email conversations and attached documents. This creates a verifiable and searchable audit trail, simplifying compliance reporting, internal audits, and legal discovery processes.
Threat Watch
IT Security Management
Organizations can leverage Threat Watch to enhance their IT security management processes. By utilizing automated assessments and real-time insights, IT security teams can promptly address vulnerabilities and maintain a robust security posture.
Risk Assessment and Compliance
Risk management teams can utilize Threat Watch to conduct thorough risk assessments that align with regulatory compliance requirements. By efficiently identifying vulnerabilities and exposures, organizations can ensure they meet industry standards and avoid potential penalties.
Incident Response Planning
Threat Watch proves invaluable in incident response planning by providing organizations with critical insights into potential threats. By knowing where their vulnerabilities lie, businesses can develop effective response strategies and minimize the impact of a cyber incident.
Employee Security Training
Organizations can use Threat Watch to identify common phishing addresses and compromised credentials, which can inform employee training programs. By educating staff about these threats, businesses can foster a culture of security awareness and reduce the likelihood of successful attacks.
Overview
About iGPT
iGPT is an advanced email intelligence API engineered specifically for enterprises and agentic workflows, fundamentally transforming how organizations access and utilize their email communications. It addresses a critical gap in the AI landscape, where email—the primary medium for real business work—often remains a siloed and unstructured data source that breaks conventional AI tools. By leveraging state-of-the-art AI capabilities, iGPT provides a secure and efficient gateway to distill meaningful, context-aware insights from vast amounts of complex email data, including lengthy conversations and embedded attachments like PDFs, documents, and spreadsheets. Its core value proposition is a unified, single API call that replaces the entire complex pipeline of parsing, chunking, indexing, and prompt tuning required by traditional RAG (Retrieval-Augmented Generation) systems. This makes it an indispensable tool for developers building intelligent agents and for industries where compliance, data integrity, and operational efficiency are paramount. With features like real-time ingestion, hybrid retrieval, and full citation of sources, iGPT enables enhanced decision-making, sophisticated workflow automation, and robust audit trails, all while maintaining enterprise-grade security with zero data training and retention policies.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform designed to provide organizations with a comprehensive overview of their cyber health. With the increasing prevalence of cyber threats, businesses need a reliable tool that can analyze their critical assets, vulnerabilities, and exposures in real-time. Threat Watch fulfills this need by empowering IT security professionals, risk management teams, and organizational leaders with the insights required to make informed decisions regarding their cybersecurity posture. The main value proposition of Threat Watch lies in its capability to deliver automated assessments and real-time insights, enabling users to swiftly identify, prioritize, and mitigate potential risks. By focusing on essential elements such as compromised credentials, breached accounts, phishing addresses, and dark web content, Threat Watch becomes an indispensable resource in the relentless fight against cyber threats. By integrating this powerful solution, organizations can significantly enhance their security measures, ensure compliance with regulatory standards, and ultimately protect their digital assets from evolving cyber risks.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is architected with enterprise-grade security as a core principle. It operates on a strict zero-data training and zero-data retention model, meaning your data is never used to train AI models, improve services, or stored after processing. All inferences are handled in memory. Access is controlled via OAuth and Role-Based Access Control (RBAC), and every API request generates a full audit trail, ensuring data sovereignty and compliance with stringent regulatory standards.
What makes iGPT different from building my own RAG system for emails?
Building a custom RAG system for emails requires significant engineering effort: parsing complex MIME data, chunking text, managing vector databases, tuning retrieval algorithms, reconstructing threads, and continuously optimizing prompts. iGPT abstracts all this complexity into a single API call. It handles real-time ingestion, hybrid retrieval, context optimization, and citation automatically, allowing developers to focus on building their application logic rather than maintaining a fragile data pipeline.
What types of email sources and attachments does iGPT support?
iGPT can connect to and deeply index data from major enterprise email providers and protocols. Its advanced attachment processing engine supports a wide range of file formats, including but not limited to PDFs, Microsoft Office documents (Word, Excel, PowerPoint), plain text files, and spreadsheets. It extracts not just raw text but also understands data structure and context within these files in relation to the email thread.
Can I control the quality and speed of the responses?
Yes, iGPT offers configurable quality tiers through its Context Engineering Framework (CEF). Users can select different CEF levels (e.g., cef-1-normal) in their API request to balance response latency, cost, and depth of analysis. This allows for optimization based on the use case, whether it requires sub-second retrieval for simple queries or deeper, more comprehensive reasoning for complex analytical tasks.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes across various industries. It is particularly beneficial for IT security professionals, risk management teams, and organizational leaders who require comprehensive cybersecurity insights.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to continuously scan the dark web for compromised credentials and sensitive information related to its users. This proactive monitoring helps organizations stay informed about potential threats.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security tools and systems within an organization. By integrating seamlessly, it enhances the overall cybersecurity framework, providing users with a more comprehensive view of their cyber health.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to evaluate its capabilities. This allows potential users to experience the platform's features and benefits before making a commitment.
Alternatives
iGPT Alternatives
iGPT is an advanced email intelligence API that falls within the Business Intelligence category. It transforms organizational email data into context-aware, actionable insights through a secure gateway, enhancing decision-making and workflow automation for enterprises. Users may explore alternatives for various reasons, including specific budget constraints, the need for different feature sets like enhanced analytics or broader data source integration, or platform compatibility requirements such as a preference for on-premise deployment over a cloud API. The search for a different solution often stems from unique organizational needs not fully addressed by a single provider. When evaluating alternatives, key considerations should include the depth of AI and natural language processing capabilities, the robustness of security and compliance frameworks, the ease and flexibility of integration, and the overall scalability of the solution to handle an enterprise's email volume and complexity.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence tool designed to help organizations evaluate their cyber health comprehensively. It falls under the category of business intelligence, specifically focused on cybersecurity. Businesses often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. As organizations evaluate their options, it’s essential to consider factors such as the level of automation, the comprehensiveness of threat coverage, integration capabilities, and user-friendliness of the alternative solutions. When choosing an alternative to Threat Watch, users should look for tools that provide real-time monitoring and automated risk assessments, similar to the features offered by Threat Watch. A strong focus on dark web monitoring and phishing detection can also enhance the effectiveness of the chosen solution. Additionally, considering the ease of implementation and the support offered by the vendor can significantly impact the overall user experience and effectiveness of the cybersecurity strategy.
