CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
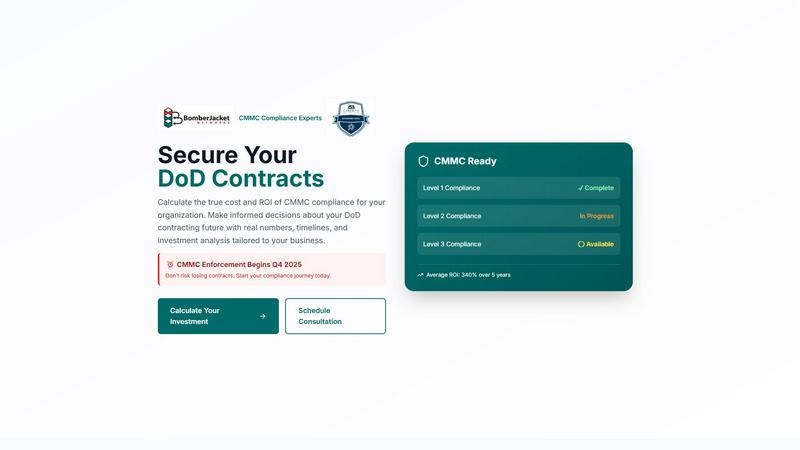
CMMC ROI
CMMC ROI calculates your compliance costs and investment returns for DoD contracts.
Last updated: March 1, 2026
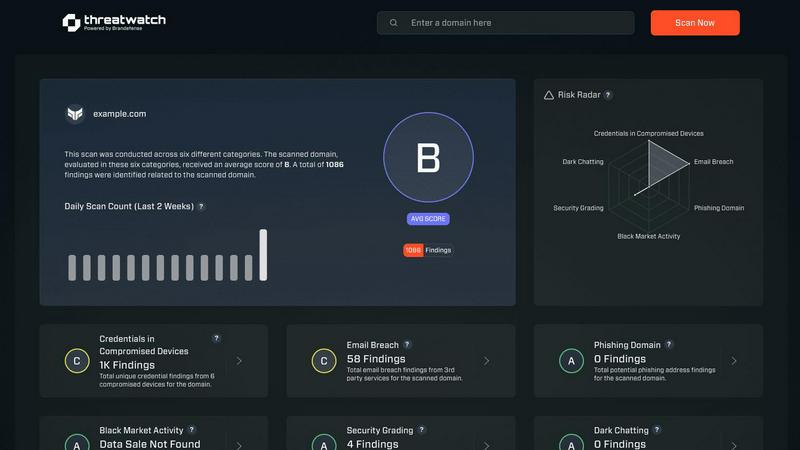
Threat Watch
Threat Watch swiftly evaluates your cybersecurity health by identifying vulnerabilities in compromised accounts and.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Personalized 5-Year Investment Calculator
This core feature allows users to input their unique business variables, including company size, DoD contract revenue, target CMMC level, and current compliance progress. The tool then processes this data against proprietary cost models to generate a tailored, comprehensive 5-year financial projection. This includes a total investment range accounting for implementation, annual maintenance, and triennial recertification costs, providing a realistic and actionable budget forecast for strategic planning.
Detailed ROI and Payback Period Analysis
Moving beyond simple cost estimation, the tool performs a sophisticated financial analysis to calculate the projected Return on Investment (ROI) and the precise payback period. It factors in the total value of DoD contracts protected from loss and models an average cost avoidance for data breaches and false claims. This transforms compliance from a line-item cost into a measurable investment, showing users the specific month they will break even and the potential multi-year financial return.
Visual ROI Timeline Projection
The tool provides a dynamic, graphical timeline that visually plots cumulative investment against cumulative returns over a 60-month period. This chart clearly illustrates the cash flow impact, pinpointing the break-even point and demonstrating how the protected contract value and cost avoidance steadily outpace the compliance investment, making the financial argument intuitive and compelling for executive stakeholders.
Strategic Risk Assessment and Compliance Roadmap
Beyond finances, the feature set includes a critical risk assessment dashboard that quantifies the contract loss risk (100% without certification) and competitor disadvantage. It also provides a detailed, phase-gated 12-month implementation timeline for CMMC Level 2, outlining key stages from Gap Assessment to Final Certification. This offers both a strategic risk perspective and a practical project management roadmap.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch offers a holistic evaluation of an organization's cybersecurity landscape. This feature analyzes critical security categories, providing users with a detailed understanding of their cyber health and highlighting vulnerabilities that need immediate attention.
Real-Time Insights and Alerts
With its real-time monitoring capabilities, Threat Watch continuously scans for potential threats and vulnerabilities. Users receive instant alerts when issues arise, allowing them to respond quickly and effectively to mitigate risks before they escalate.
Dark Web Monitoring
One of the standout features of Threat Watch is its ability to monitor the dark web for compromised credentials and sensitive information. This proactive approach helps organizations stay ahead of potential threats and protects their valuable data from being exploited by malicious actors.
Automated Risk Assessments
Threat Watch automates the process of risk assessment, enabling organizations to quickly identify and prioritize potential vulnerabilities. This efficiency not only saves time but also ensures that security teams can focus their efforts on the most critical issues affecting their cybersecurity posture.
Use Cases
CMMC ROI
Executive Budget Justification and Board Reporting
Company leadership and financial officers use the tool to generate concrete, data-backed reports to justify the significant upfront investment in CMMC compliance to boards of directors, investors, or internal budget committees. The clear ROI projections and payback timeline turn a complex security mandate into a defensible business case for capital allocation.
Strategic Business Development and Bid Planning
Business development and capture teams utilize the analysis to understand how CMMC certification impacts competitive positioning. By quantifying the "win rate increase" advantage, they can strategically pursue contracts that require certification, using the tool's outputs to inform bid/no-bid decisions and proposal strategies that highlight their certified status.
Compliance Program Scoping and Vendor Management
IT security managers and CISOs employ the tool to scope the size and scale of their required compliance program. The detailed cost breakdown helps in creating RFPs for managed service providers or C3PAOs, setting realistic budgets for internal projects, and managing stakeholder expectations regarding the timeline and resource commitment needed.
Proactive Risk Management and Contract Protection
Contract administrators and legal teams leverage the risk assessment features to understand the profound financial and contractual implications of non-compliance. The tool quantifies the direct risk to existing DoD revenue, providing a powerful impetus for proactive investment to mitigate the risk of contract termination and associated legal liabilities.
Threat Watch
IT Security Management
Organizations can leverage Threat Watch to enhance their IT security management processes. By utilizing automated assessments and real-time insights, IT security teams can promptly address vulnerabilities and maintain a robust security posture.
Risk Assessment and Compliance
Risk management teams can utilize Threat Watch to conduct thorough risk assessments that align with regulatory compliance requirements. By efficiently identifying vulnerabilities and exposures, organizations can ensure they meet industry standards and avoid potential penalties.
Incident Response Planning
Threat Watch proves invaluable in incident response planning by providing organizations with critical insights into potential threats. By knowing where their vulnerabilities lie, businesses can develop effective response strategies and minimize the impact of a cyber incident.
Employee Security Training
Organizations can use Threat Watch to identify common phishing addresses and compromised credentials, which can inform employee training programs. By educating staff about these threats, businesses can foster a culture of security awareness and reduce the likelihood of successful attacks.
Overview
About CMMC ROI
CMMC ROI is a sophisticated, data-driven strategic planning and financial analysis tool developed by BomberJacket Networks, an authorized C3PAO and service-disabled veteran-owned business. It is engineered specifically for the ecosystem of Department of Defense (DoD) contractors and subcontractors who are mandated to achieve Cybersecurity Maturity Model Certification (CMMC). The product's core function is to demystify the complex and often intimidating process of CMMC compliance by translating abstract security requirements into clear, quantifiable business and financial metrics. By allowing organizations to input specific parameters—such as company size, annual DoD revenue, required CMMC level, and current compliance status—the tool generates a personalized, comprehensive analysis. This includes a detailed 5-year total investment range, projected Return on Investment (ROI), payback period, and a visual timeline mapping expenditures against protected contract value. Its primary value proposition is empowering defense contractors to transition from a state of uncertainty and perceived cost burden to a strategic, informed perspective. It frames CMMC compliance not as an expense but as a critical business investment that protects existing revenue streams, unlocks new contract opportunities by providing a competitive advantage, and mitigates substantial financial risks associated with data breaches and False Claims Act violations, all ahead of the critical CMMC enforcement deadline commencing in Q4 2025.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform designed to provide organizations with a comprehensive overview of their cyber health. With the increasing prevalence of cyber threats, businesses need a reliable tool that can analyze their critical assets, vulnerabilities, and exposures in real-time. Threat Watch fulfills this need by empowering IT security professionals, risk management teams, and organizational leaders with the insights required to make informed decisions regarding their cybersecurity posture. The main value proposition of Threat Watch lies in its capability to deliver automated assessments and real-time insights, enabling users to swiftly identify, prioritize, and mitigate potential risks. By focusing on essential elements such as compromised credentials, breached accounts, phishing addresses, and dark web content, Threat Watch becomes an indispensable resource in the relentless fight against cyber threats. By integrating this powerful solution, organizations can significantly enhance their security measures, ensure compliance with regulatory standards, and ultimately protect their digital assets from evolving cyber risks.
Frequently Asked Questions
CMMC ROI FAQ
How does the CMMC ROI calculator determine its cost ranges?
The cost ranges are derived from BomberJacket Networks' extensive experience as an authorized C3PAO and service provider, incorporating real-world data from assessments and implementations. Costs are modeled based on company size tiers, the specific CMMC level required, and industry-standard efforts for implementing security controls, developing System Security Plans (SSPs), and undergoing official assessments. The ranges account for variables in organizational complexity and existing security posture.
What is included in the "Protected Value" for the ROI calculation?
The Protected Value is a key metric comprising two main components. First, it includes the total value of the user's DoD contract revenue over the 5-year analysis period, representing the revenue safeguarded from loss due to non-compliance. Second, it incorporates an average cost avoidance figure (e.g., $2.5M) for a potential data breach or False Claims Act penalty, which CMMC controls help mitigate. This combined value is weighed against the total compliance investment.
Can the tool account for our company's current compliance progress?
Yes, the calculator includes a "Current Compliance Status" selector with options such as "Not Started," "In Progress," and "Nearly Complete." Selecting a status beyond "Not Started" applies a progressive discount (e.g., 30% off for "In Progress," 60% off for "Nearly Complete") to the implementation cost estimate. This provides a more accurate and personalized investment forecast that reflects work already accomplished.
Why is the payback period often shown to be relatively short?
The payback period can be short—often shown as under one year—because the tool models the immediate and severe risk of losing 100% of DoD contract revenue if certification is not achieved by the enforcement deadline. When the annual value of protected contracts is substantial, the investment in certification is quickly offset by the prevention of that total revenue loss, in addition to the avoided costs of potential security incidents.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes across various industries. It is particularly beneficial for IT security professionals, risk management teams, and organizational leaders who require comprehensive cybersecurity insights.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to continuously scan the dark web for compromised credentials and sensitive information related to its users. This proactive monitoring helps organizations stay informed about potential threats.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security tools and systems within an organization. By integrating seamlessly, it enhances the overall cybersecurity framework, providing users with a more comprehensive view of their cyber health.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to evaluate its capabilities. This allows potential users to experience the platform's features and benefits before making a commitment.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence tool designed for defense contractors, specifically a data-driven investment calculator for Cybersecurity Maturity Model Certification compliance. It helps organizations quantify the costs and returns associated with meeting DoD cybersecurity mandates, translating complex requirements into clear financial metrics for strategic planning. Users may seek alternatives for various reasons, including budget constraints, a need for different feature sets like integrated compliance management, or a preference for platforms that are part of a larger enterprise software ecosystem. Some may require tools with broader IT governance capabilities beyond pure financial modeling for CMMC. When evaluating alternatives, key considerations include the tool's accuracy in cost estimation, its ability to model scenario-based outcomes, the depth of its CMMC framework knowledge, and the credibility of its data sources. The ideal solution should provide actionable intelligence that supports both compliance justification and long-term cybersecurity investment strategy.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence tool designed to help organizations evaluate their cyber health comprehensively. It falls under the category of business intelligence, specifically focused on cybersecurity. Businesses often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. As organizations evaluate their options, it’s essential to consider factors such as the level of automation, the comprehensiveness of threat coverage, integration capabilities, and user-friendliness of the alternative solutions. When choosing an alternative to Threat Watch, users should look for tools that provide real-time monitoring and automated risk assessments, similar to the features offered by Threat Watch. A strong focus on dark web monitoring and phishing detection can also enhance the effectiveness of the chosen solution. Additionally, considering the ease of implementation and the support offered by the vendor can significantly impact the overall user experience and effectiveness of the cybersecurity strategy.
