Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy provides comprehensive AI governance for compliance, risk management, and real-time oversight.
Last updated: March 1, 2026
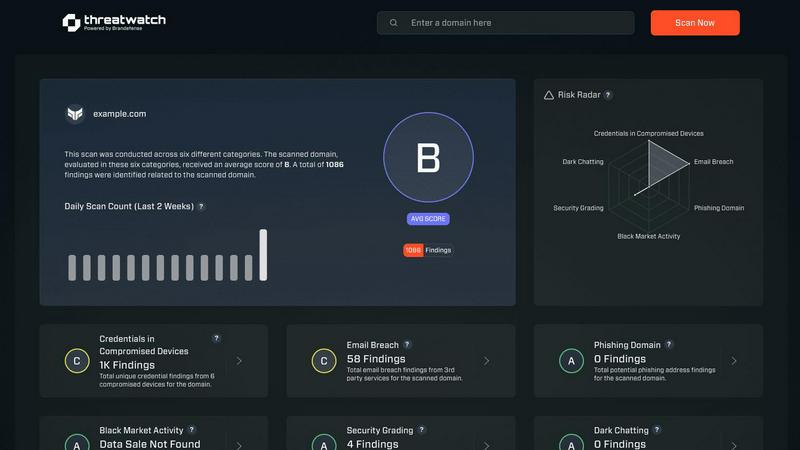
Threat Watch
Threat Watch swiftly evaluates your cybersecurity health by identifying vulnerabilities in compromised accounts and.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
This feature provides complete visibility across an organization's entire AI ecosystem. It allows teams to discover, document, and onboard every AI system—whether built in-house, sourced from vendors, or embedded in other software—into a centralized registry. By connecting to existing MLOps and GenAI platforms, it eliminates blind spots without requiring costly migrations. This creates a single source of truth for all AI assets, which is the foundational step for effective governance, risk assessment, and compliance reporting.
Control Frameworks
Deeploy simplifies regulatory navigation with pre-built and customizable control frameworks. Organizations can adopt industry-standard frameworks like ISO 42001 or the NIST AI RMF, or build their own tailored policies. The platform guides users through risk classification processes, establishing clear accountability with defined approval workflows. This structured approach demystifies complex regulations, turning abstract requirements into manageable, step-by-step processes that ensure consistent application of governance rules across all AI initiatives.
Control Implementation
This feature translates governance policies into actionable, engineer-friendly requirements. Instead of presenting vague guidelines, Deeploy provides clear technical and procedural controls for each AI system based on its risk profile. It dramatically accelerates compliance—by up to 90% according to the provider—through the use of templates and automated evidence collection. It even employs AI-powered assessments to handle repetitive compliance tasks, ensuring that governance is practically implemented and followed by engineering teams.
Real-Time Monitoring and Explainability
Deeploy offers continuous, production-level monitoring to proactively prevent AI incidents. It tracks model performance, data drift, and output anomalies, sending instant alerts when issues are detected. Crucially, it includes built-in explainability features that help users understand why a model made a specific prediction. For LLMs, it adds tracing and guardrails to protect outputs. This continuous oversight allows teams to identify and rectify errors before they impact end-users or create compliance breaches.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch offers a holistic evaluation of an organization's cybersecurity landscape. This feature analyzes critical security categories, providing users with a detailed understanding of their cyber health and highlighting vulnerabilities that need immediate attention.
Real-Time Insights and Alerts
With its real-time monitoring capabilities, Threat Watch continuously scans for potential threats and vulnerabilities. Users receive instant alerts when issues arise, allowing them to respond quickly and effectively to mitigate risks before they escalate.
Dark Web Monitoring
One of the standout features of Threat Watch is its ability to monitor the dark web for compromised credentials and sensitive information. This proactive approach helps organizations stay ahead of potential threats and protects their valuable data from being exploited by malicious actors.
Automated Risk Assessments
Threat Watch automates the process of risk assessment, enabling organizations to quickly identify and prioritize potential vulnerabilities. This efficiency not only saves time but also ensures that security teams can focus their efforts on the most critical issues affecting their cybersecurity posture.
Use Cases
Deeploy
Regulatory Compliance and Audit Readiness
Organizations subject to regulations like the EU AI Act use Deeploy to systematically achieve and demonstrate compliance. The platform automates evidence collection, maintains detailed audit trails, and provides documentation for every AI system. This use case is critical for enterprises in heavily regulated industries such as finance, healthcare, and public services, enabling them to scale AI with confidence while having all necessary proof for regulatory audits readily available.
Centralized AI Inventory and Risk Management
Companies with scattered AI deployments across multiple teams and vendors utilize Deeploy to create a unified inventory. This central registry allows leadership and risk officers to gain a holistic view of their AI exposure, classify systems by risk level, and apply appropriate governance controls consistently. It transforms AI from an unmanaged collection of tools into a strategically overseen portfolio, enabling informed decision-making and proactive risk mitigation.
Accelerating Safe Model Deployment
Data science and MLOps teams employ Deeploy to streamline the path from development to production. By integrating governance checks and monitoring capabilities directly into the deployment pipeline, the platform reduces deployment time from weeks to hours while ensuring new models meet all organizational standards. The built-in explainability features also facilitate smoother handovers and provide transparency for both technical and non-technical stakeholders.
Ensuring Ethical AI and Human Oversight
In sensitive applications like mental healthcare or customer-facing services, Deeploy facilitates responsible AI implementation. It enforces ethical guidelines through customizable control frameworks and enables essential human-in-the-loop processes. The real-time explainability and feedback mechanisms allow human experts to review, understand, and correct AI decisions, building trust and ensuring systems operate within defined ethical boundaries.
Threat Watch
IT Security Management
Organizations can leverage Threat Watch to enhance their IT security management processes. By utilizing automated assessments and real-time insights, IT security teams can promptly address vulnerabilities and maintain a robust security posture.
Risk Assessment and Compliance
Risk management teams can utilize Threat Watch to conduct thorough risk assessments that align with regulatory compliance requirements. By efficiently identifying vulnerabilities and exposures, organizations can ensure they meet industry standards and avoid potential penalties.
Incident Response Planning
Threat Watch proves invaluable in incident response planning by providing organizations with critical insights into potential threats. By knowing where their vulnerabilities lie, businesses can develop effective response strategies and minimize the impact of a cyber incident.
Employee Security Training
Organizations can use Threat Watch to identify common phishing addresses and compromised credentials, which can inform employee training programs. By educating staff about these threats, businesses can foster a culture of security awareness and reduce the likelihood of successful attacks.
Overview
About Deeploy
Deeploy is a comprehensive AI governance and operational platform designed to provide organizations with the critical infrastructure needed to manage, monitor, and scale artificial intelligence systems responsibly. In an era of rapid AI proliferation, organizations often struggle with fragmented AI tools, models, and vendors, leading to significant operational, compliance, and reputational risks. Deeploy directly addresses this challenge by centralizing oversight of an entire AI landscape into a single, unified system. Its core value proposition is enabling businesses to harness the transformative power of AI while maintaining complete control, ensuring accountability, and adhering to evolving regulatory standards like the EU AI Act. The platform is built for enterprises running AI at scale, including data science teams, ML engineers, compliance officers, and risk management executives. By integrating governance directly into the AI lifecycle, Deeploy transforms governance from a bureaucratic hurdle into an enabling framework that accelerates safe deployment, provides real-time explainability, and builds essential trust in AI operations across all teams and use cases.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform designed to provide organizations with a comprehensive overview of their cyber health. With the increasing prevalence of cyber threats, businesses need a reliable tool that can analyze their critical assets, vulnerabilities, and exposures in real-time. Threat Watch fulfills this need by empowering IT security professionals, risk management teams, and organizational leaders with the insights required to make informed decisions regarding their cybersecurity posture. The main value proposition of Threat Watch lies in its capability to deliver automated assessments and real-time insights, enabling users to swiftly identify, prioritize, and mitigate potential risks. By focusing on essential elements such as compromised credentials, breached accounts, phishing addresses, and dark web content, Threat Watch becomes an indispensable resource in the relentless fight against cyber threats. By integrating this powerful solution, organizations can significantly enhance their security measures, ensure compliance with regulatory standards, and ultimately protect their digital assets from evolving cyber risks.
Frequently Asked Questions
Deeploy FAQ
What is AI governance and why is it important?
AI governance refers to the framework of policies, processes, and tools used to ensure AI systems are developed and deployed responsibly, ethically, and in compliance with regulations. It is critically important because ungoverned AI can lead to significant risks including biased outcomes, security vulnerabilities, regulatory fines, and loss of public trust. Deeploy provides the infrastructure to operationalize governance, turning high-level principles into enforceable, day-to-day practices that mitigate risk while enabling innovation.
How does Deeploy handle different types of AI models?
Deeploy is designed as a platform-agnostic solution capable of governing diverse AI systems. It can connect to and manage traditional machine learning models from MLOps platforms, generative AI models from various vendors, and AI embedded within third-party software. The system applies relevant controls and monitoring based on each model's specific risk classification and use case, providing a consistent governance layer across an organization's entire heterogeneous AI landscape.
Can Deeploy help with compliance with the EU AI Act?
Yes, Deeploy is explicitly built to help organizations comply with the EU AI Act and other global regulations. It provides workflows to classify AI systems according to the Act's risk categories (unacceptable, high, limited, minimal), implements corresponding required controls for high-risk systems, and automates the documentation and evidence collection needed to demonstrate compliance. The control frameworks can be tailored to map directly to the Act's specific requirements.
How does the real-time monitoring feature work?
Deeploy's real-time monitoring continuously tracks key performance indicators of deployed AI models. It monitors for concept drift, data drift, performance degradation, and output anomalies. When a metric deviates beyond a predefined threshold, the system triggers instant alerts to relevant teams. For generative AI, it includes tracing to log the chain of reasoning and can apply guardrails to filter or flag inappropriate outputs, allowing issues to be addressed proactively before affecting users.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes across various industries. It is particularly beneficial for IT security professionals, risk management teams, and organizational leaders who require comprehensive cybersecurity insights.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to continuously scan the dark web for compromised credentials and sensitive information related to its users. This proactive monitoring helps organizations stay informed about potential threats.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security tools and systems within an organization. By integrating seamlessly, it enhances the overall cybersecurity framework, providing users with a more comprehensive view of their cyber health.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to evaluate its capabilities. This allows potential users to experience the platform's features and benefits before making a commitment.
Alternatives
Deeploy Alternatives
Deeploy is a specialized AI governance platform within the business intelligence and enterprise software category. It provides organizations with the tools to oversee, monitor, and ensure compliance for their AI systems, addressing critical needs around risk management and regulatory adherence like the EU AI Act. Users may explore alternatives to Deeploy for various reasons. Common considerations include specific budgetary constraints, the need for different feature integrations, or a requirement for a platform that aligns with a particular technical stack or existing workflow. The search often stems from a need to find the optimal balance between comprehensive governance capabilities and operational fit. When evaluating alternatives, key factors to assess include the depth of AI model lifecycle coverage, the flexibility of compliance frameworks offered, the strength of audit and explainability features, and the overall ease of integration with an organization's current MLOps and data science ecosystems. The goal is to identify a solution that provides robust oversight without creating unnecessary complexity.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence tool designed to help organizations evaluate their cyber health comprehensively. It falls under the category of business intelligence, specifically focused on cybersecurity. Businesses often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. As organizations evaluate their options, it’s essential to consider factors such as the level of automation, the comprehensiveness of threat coverage, integration capabilities, and user-friendliness of the alternative solutions. When choosing an alternative to Threat Watch, users should look for tools that provide real-time monitoring and automated risk assessments, similar to the features offered by Threat Watch. A strong focus on dark web monitoring and phishing detection can also enhance the effectiveness of the chosen solution. Additionally, considering the ease of implementation and the support offered by the vendor can significantly impact the overall user experience and effectiveness of the cybersecurity strategy.
