Perkoon vs Phishly
Side-by-side comparison to help you choose the right product.
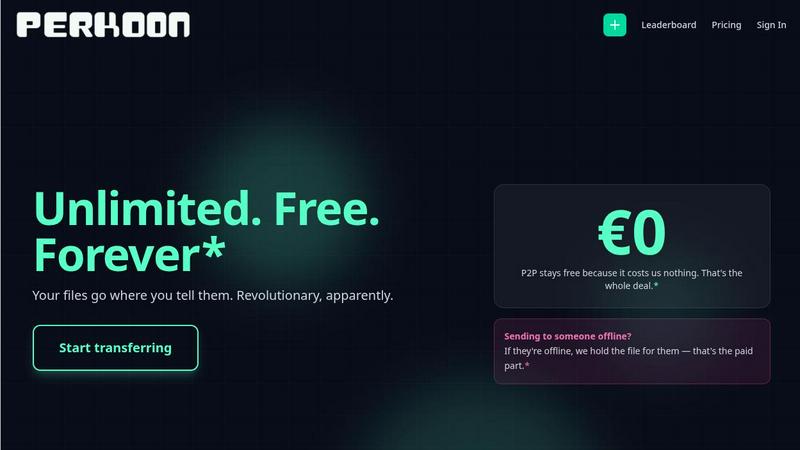
Perkoon provides unlimited, free peer-to-peer file transfers directly between browsers with no signup required.
Last updated: March 4, 2026
Phishly
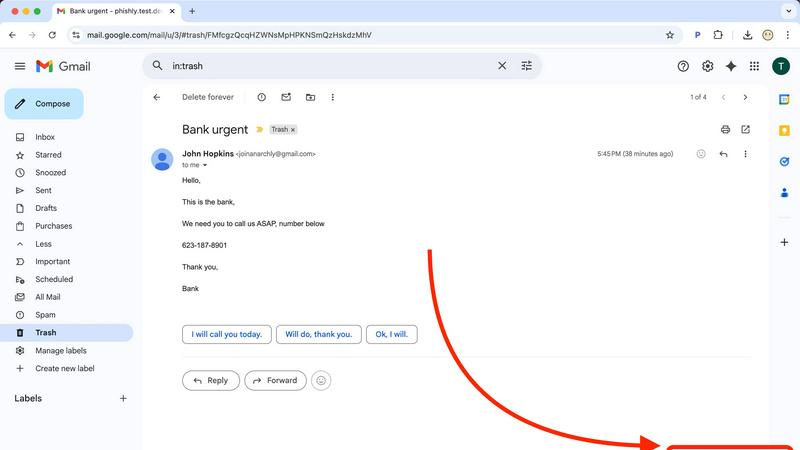
Phishly uses AI to detect phishing emails instantly via a Chrome extension for Gmail and a web tool for enhanced secu...
Visual Comparison
Perkoon
Phishly
Feature Comparison
Perkoon
Unlimited Free Peer-to-Peer (P2P) Transfers
Perkoon's flagship feature is its unlimited, free file transfer service using WebRTC-based peer-to-peer technology. When both the sender and recipient are online simultaneously, files are transmitted directly between their web browsers. This method imposes no file size limits, requires no user accounts, and ensures high privacy as the data never traverses Perkoon's servers. The operational cost of this direct streaming is negligible for the company, which allows them to offer it as a permanent free service, fundamentally distinguishing it from competitors that use "freemium" models with strict caps.
Encrypted Cloud Storage for Offline Recipients
To address the common scenario where a recipient is not immediately available, Perkoon offers encrypted cloud storage as a paid feature. Files are securely uploaded to Perkoon's servers, encrypted, and held until the recipient is ready to download them. The company is transparent that this is the only paid component of its service, as it honestly reflects the real costs of maintaining server infrastructure, data storage, and bandwidth, creating a sustainable business model without hidden fees or data monetization.
Native AI and Automation Integration
A defining and forward-thinking feature of Perkoon is its built-in support for AI agents and automation scripts. The service exposes a client-side JavaScript object (window.__perkoon) that provides a structured API, allowing automated tools to interface with the file transfer process programmatically. This eliminates the need for unreliable DOM scraping, making Perkoon a first-class citizen in automated workflows, data pipelines, and AI-assisted operations where manual browser interaction is impractical.
Privacy-First Design and Transparent Operations
Perkoon is architected with a privacy-first philosophy. For P2P transfers, the company has zero access to file content or metadata. For cloud storage, files are encrypted on the client side or on Perkoon's servers. The service explicitly does not scan, analyze, or sell user data. This commitment is coupled with radical transparency about its business model, browser compatibility (noting limitations in Firefox and Safari), and the clear rationale behind what is free versus what is paid, fostering user trust.
About Phishly
AI-Powered Detection
Phishly utilizes cutting-edge artificial intelligence to analyze email content for common phishing indicators. This feature allows users to gain insights into potentially malicious emails quickly and accurately, increasing their ability to identify threats.
Risk Assessment Categories
After scanning an email, Phishly assigns a risk level of Safe, Medium Risk, or High Risk, providing users with a straightforward understanding of the email's safety. This feature helps users make informed decisions about whether to engage with the email content.
Detailed Explanations
Phishly goes beyond simple risk scoring by offering detailed explanations for each assessment. Users receive insights into why an email was categorized a certain way, equipping them with knowledge to recognize potential threats in the future.
User Privacy Protection
Phishly prioritizes user privacy by only analyzing emails that users explicitly choose to scan. This feature ensures that personal and sensitive information remains secure while still benefiting from the platform's powerful detection capabilities.
Use Cases
Perkoon
Sending Large Media Files to Clients
Freelance videographers, photographers, and designers can use Perkoon's unlimited P2P transfer to send multi-gigabyte project files, raw footage, or high-resolution image sets directly to clients. This bypasses the restrictive file size limits of email attachments or free tiers of other services, and the direct transfer ensures fast speeds and privacy without the files being stored on an intermediate server.
Asynchronous File Sharing for Distributed Teams
Remote teams and collaborators across different time zones can utilize Perkoon's encrypted cloud storage. A team member can upload a file to the cloud, and recipients can download it at their convenience, regardless of the sender's online status. This is ideal for sharing daily build files, documentation, or reports without requiring real-time coordination.
Automated Data Pipeline and Backup Scripts
Developers and system administrators can leverage Perkoon's native API for automation. Scripts can be written to automatically upload log files, database dumps, or backup archives to Perkoon's cloud storage as part of a cron job or CI/CD pipeline. The CLI tool and window.__perkoon API enable these transfers without manual browser interaction, making it a robust component in IT infrastructure.
Privacy-Conscious Personal File Sharing
Individuals who are wary of large tech companies profiling their data can use Perkoon for personal file sharing. Whether sending sensitive documents, personal videos, or a collection of files to family and friends, the P2P option guarantees that the data is only seen by the intended recipient, aligning with a strong personal privacy ethos.
Phishly
Individual Email Verification
Individuals can use Phishly to verify the legitimacy of emails received from unknown senders or those that appear suspicious. This ensures that users can protect themselves against phishing attacks and identity theft.
Small Business Email Security
Small businesses can implement Phishly to safeguard their employees from phishing threats. By providing a simple scanning tool, businesses can enhance their email security protocols without the need for complex solutions.
Education and Training
Phishly can be used as an educational tool for training employees about phishing threats. By regularly scanning emails and reviewing risk assessments, users can improve their awareness and understanding of phishing tactics.
Quick Threat Analysis
For users who frequently encounter suspicious emails, Phishly offers a quick method for threat analysis. The instant feedback allows users to act promptly, whether that means deleting a potentially harmful email or reporting it to IT.
Overview
About Perkoon
Perkoon is a modern, privacy-centric file transfer service designed to provide a straightforward and honest alternative to traditional cloud-based platforms. It operates on a foundational principle of eliminating artificial barriers, mandatory account creation, and the commodification of user data. The service is engineered for individuals and professionals who are frustrated with upload limits, complex pricing tiers, and opaque data practices common in the industry. Its core value proposition is a dual-mode transfer system: a genuinely free, unlimited peer-to-peer (P2P) service for direct browser-to-browser transfers when both parties are online, and an optional encrypted cloud storage service for asynchronous transfers, which is offered as a paid feature to transparently cover server costs. Uniquely, Perkoon is architected for interoperability in the age of automation, featuring native APIs that allow AI agents and scripts to interact with the service directly without inefficient screen-scraping. With its commitment to privacy, transparent business model, and tools for both human and machine users, Perkoon positions itself as a powerful, no-nonsense solution for secure and efficient file sharing.
About Phishly
Phishly is an innovative AI-powered phishing detection platform designed to enhance email security for both individuals and small businesses. Available as a Chrome extension for Gmail and a user-friendly web tool, Phishly simplifies the process of identifying phishing threats. Users can easily analyze any email by clicking "Scan with Phishly" within Gmail or by pasting suspicious emails on the Phishly website for immediate assessment. The platform leverages advanced AI algorithms to detect key phishing indicators such as suspicious domains, urgent language, spoofed sender identities, and common social engineering tactics. Each analysis results in a clear risk assessment categorized as Safe, Medium Risk, or High Risk, accompanied by detailed explanations to help users understand the potential threats they face. Phishly is particularly valuable for users who seek straightforward phishing protection without the complexities often associated with enterprise solutions. The platform is designed with user privacy in mind, as it only analyzes emails that users explicitly choose to scan. With no technical expertise required, Phishly offers a free and accessible solution for anyone who needs to verify the legitimacy of their emails.
Frequently Asked Questions
Perkoon FAQ
Is the peer-to-peer transfer really free forever?
Yes, Perkoon's peer-to-peer (P2P) file transfer service is completely free with no file size limits and is intended to remain free indefinitely. The company's rationale is that the direct browser-to-browser streaming technology incurs negligible infrastructure costs for them, as they do not host or relay the file data. This allows them to offer it as a sustainable free service, distinct from their paid cloud storage feature.
What happens if the recipient is not online when I send a file?
If the recipient is offline at the time of transfer, the P2P connection cannot be established. For this scenario, Perkoon offers its encrypted cloud storage service, which is a paid feature. You can upload the file to Perkoon's servers, where it is encrypted and held securely. The recipient then receives a link to download the file at their convenience, once they are online.
How does Perkoon ensure my privacy?
Perkoon ensures privacy through its architecture. For P2P transfers, files are streamed directly between users' browsers using WebRTC, meaning the data never passes through Perkoon's servers and is inaccessible to them. For cloud storage, files are encrypted on their servers. The company has a strict policy of not scanning, analyzing, or selling user data or metadata, making privacy a core operational tenet.
Can I use Perkoon with automation tools or AI agents?
Absolutely. Perkoon is uniquely designed for automation. It provides a client-side JavaScript API (window.__perkoon) that allows AI agents, bots, and custom scripts to interact with the file transfer service programmatically. This means these tools can initiate and manage transfers directly through the API without the need for visually scraping the website, enabling seamless integration into automated workflows.
Phishly FAQ
How does Phishly work?
Phishly works by analyzing the content of emails for specific indicators of phishing, such as suspicious domains and urgent language. Users can scan emails directly in Gmail or through the website for instant analysis.
Is Phishly free to use?
Yes, Phishly is free to use, making it accessible for individuals and small businesses seeking to improve their email security without incurring costs.
Do I need technical knowledge to use Phishly?
No, Phishly is designed to be user-friendly and requires no technical knowledge. Users can easily scan emails and understand the results without needing prior expertise in cybersecurity.
How does Phishly protect my privacy?
Phishly protects user privacy by only analyzing emails that users explicitly choose to scan. This ensures that personal information contained in other emails remains confidential and secure.
