Karolium vs Threat Watch
Side-by-side comparison to help you choose the right product.
Karolium is a zero-code platform that enables rapid customization of enterprise applications for seamless digital.
Last updated: February 28, 2026
Threat Watch
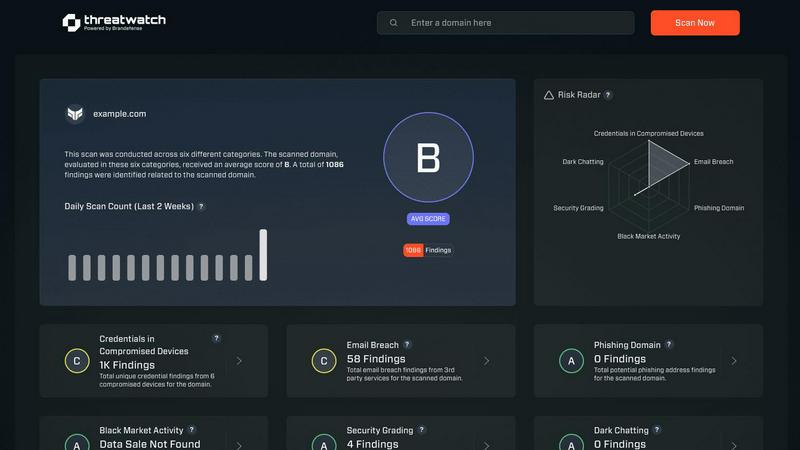
Threat Watch swiftly evaluates your cybersecurity health by identifying vulnerabilities in compromised accounts and.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Development
Karolium offers a truly unified zero-code environment that allows users to design and customize applications without any programming knowledge. This feature significantly reduces the time and resources needed for application development, enabling organizations to respond quickly to changing business demands.
Pre-Composed Modules
The platform includes a library of ready-to-use, pre-composed modules that can be easily integrated into existing applications. These modules cover a range of functionalities, allowing businesses to augment their application ecosystems and create tailored workflows quickly and efficiently.
Built-In AI Capabilities
Karolium incorporates advanced artificial intelligence features, providing predictive and prescriptive analytics that help organizations anticipate trends and make informed decisions. This functionality enhances the intelligence of business applications, driving strategic evolution and improved operational outcomes.
Seamless Integration
Designed to work harmoniously with both legacy systems and modern microservices, Karolium ensures that organizations can maintain operational continuity while adopting new technologies. This feature allows for the easy integration of AI-driven applications into existing workflows, maximizing the value of current investments.
About Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch offers a holistic evaluation of an organization's cybersecurity landscape. This feature analyzes critical security categories, providing users with a detailed understanding of their cyber health and highlighting vulnerabilities that need immediate attention.
Real-Time Insights and Alerts
With its real-time monitoring capabilities, Threat Watch continuously scans for potential threats and vulnerabilities. Users receive instant alerts when issues arise, allowing them to respond quickly and effectively to mitigate risks before they escalate.
Dark Web Monitoring
One of the standout features of Threat Watch is its ability to monitor the dark web for compromised credentials and sensitive information. This proactive approach helps organizations stay ahead of potential threats and protects their valuable data from being exploited by malicious actors.
Automated Risk Assessments
Threat Watch automates the process of risk assessment, enabling organizations to quickly identify and prioritize potential vulnerabilities. This efficiency not only saves time but also ensures that security teams can focus their efforts on the most critical issues affecting their cybersecurity posture.
Use Cases
Karolium
Accelerating Digital Transformation
Organizations looking to speed up their digital transformation initiatives can leverage Karolium to build and deploy applications rapidly. By eliminating the complexities of traditional coding, businesses can focus on innovation and responsiveness to market changes.
Customizing Workflows
Businesses frustrated with off-the-shelf solutions can use Karolium to create customized workflows that align with their unique operational needs. This adaptability ensures that organizations can optimize their processes without the constraints of rigid software.
Enhancing Data-Driven Decision Making
Karolium enables enterprises to harness the power of data through its built-in AI capabilities. Organizations can utilize predictive analytics to forecast trends and prescriptive analytics to recommend optimal actions, leading to more informed decision-making.
Improving Supplier Collaboration
With features designed for the new-age supply chain landscape, Karolium facilitates real-time collaboration with suppliers. Businesses can streamline procurement processes and enhance supplier relationships, improving overall supply chain efficiency.
Threat Watch
IT Security Management
Organizations can leverage Threat Watch to enhance their IT security management processes. By utilizing automated assessments and real-time insights, IT security teams can promptly address vulnerabilities and maintain a robust security posture.
Risk Assessment and Compliance
Risk management teams can utilize Threat Watch to conduct thorough risk assessments that align with regulatory compliance requirements. By efficiently identifying vulnerabilities and exposures, organizations can ensure they meet industry standards and avoid potential penalties.
Incident Response Planning
Threat Watch proves invaluable in incident response planning by providing organizations with critical insights into potential threats. By knowing where their vulnerabilities lie, businesses can develop effective response strategies and minimize the impact of a cyber incident.
Employee Security Training
Organizations can use Threat Watch to identify common phishing addresses and compromised credentials, which can inform employee training programs. By educating staff about these threats, businesses can foster a culture of security awareness and reduce the likelihood of successful attacks.
Overview
About Karolium
Karolium is an advanced, unified zero-code platform designed specifically for organizations looking to create and customize applications without the complexities associated with traditional coding. Its innovative architecture combines the capabilities of iPaaS, aPaaS, oPaaS, and AIPaaS, enabling enterprises to rapidly build, extend, and personalize intelligent business solutions. This platform provides ready-to-deploy modules that simplify the development of custom applications, making it ideal for businesses across various sectors that require agility and efficiency in their digital transformation efforts. By removing the burdens of coding, Karolium empowers users to deploy applications swiftly, enhancing their operational effectiveness. The platform's built-in predictive and prescriptive capabilities leverage artificial intelligence, facilitating smarter decision-making and strategic growth. It is particularly advantageous for enterprises frustrated by rigid off-the-shelf solutions, as it offers a customizable environment that seamlessly adapts to specific workflows and operational needs.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform designed to provide organizations with a comprehensive overview of their cyber health. With the increasing prevalence of cyber threats, businesses need a reliable tool that can analyze their critical assets, vulnerabilities, and exposures in real-time. Threat Watch fulfills this need by empowering IT security professionals, risk management teams, and organizational leaders with the insights required to make informed decisions regarding their cybersecurity posture. The main value proposition of Threat Watch lies in its capability to deliver automated assessments and real-time insights, enabling users to swiftly identify, prioritize, and mitigate potential risks. By focusing on essential elements such as compromised credentials, breached accounts, phishing addresses, and dark web content, Threat Watch becomes an indispensable resource in the relentless fight against cyber threats. By integrating this powerful solution, organizations can significantly enhance their security measures, ensure compliance with regulatory standards, and ultimately protect their digital assets from evolving cyber risks.
Frequently Asked Questions
Karolium FAQ
What types of organizations can benefit from Karolium?
Karolium is designed for a wide range of organizations, particularly those in industries looking to enhance digital transformation efforts, improve operational efficiency, and customize applications without the need for extensive coding knowledge.
How does Karolium support integration with existing systems?
Karolium is built to ensure seamless integration with both legacy systems and modern microservices applications. This feature allows businesses to adopt new technologies while maintaining continuity in their operations.
Can non-technical users effectively utilize Karolium?
Yes, Karolium is a zero-code platform specifically designed for users without programming backgrounds. Its intuitive interface and pre-composed modules empower non-technical users to build and customize applications easily.
What advantages does Karolium provide over traditional coding platforms?
Karolium eliminates the complexities and time constraints associated with traditional coding, enabling rapid application development. It also offers built-in AI capabilities and customizable modules, making it a more agile and efficient solution for enterprises.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes across various industries. It is particularly beneficial for IT security professionals, risk management teams, and organizational leaders who require comprehensive cybersecurity insights.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to continuously scan the dark web for compromised credentials and sensitive information related to its users. This proactive monitoring helps organizations stay informed about potential threats.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security tools and systems within an organization. By integrating seamlessly, it enhances the overall cybersecurity framework, providing users with a more comprehensive view of their cyber health.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to evaluate its capabilities. This allows potential users to experience the platform's features and benefits before making a commitment.
Alternatives
Karolium Alternatives
Karolium is a zero-code platform that falls under the category of enterprise application development. It allows organizations to rapidly customize and deploy applications without the need for traditional coding, thereby streamlining digital transformation initiatives. The platform is designed to enhance agility and efficiency by providing users with the tools necessary to create tailored solutions that meet their specific business requirements. Users often seek alternatives to Karolium for various reasons, including pricing, feature sets, and specific platform needs that may not be fully addressed by Karolium. When considering alternatives, it is essential to evaluate factors such as ease of customization, integration capabilities with existing systems, user accessibility, and the inclusion of advanced analytics tools. A thorough comparison of these elements will help ensure that the chosen solution aligns closely with the organization’s objectives and operational workflows.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence tool designed to help organizations evaluate their cyber health comprehensively. It falls under the category of business intelligence, specifically focused on cybersecurity. Businesses often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. As organizations evaluate their options, it’s essential to consider factors such as the level of automation, the comprehensiveness of threat coverage, integration capabilities, and user-friendliness of the alternative solutions. When choosing an alternative to Threat Watch, users should look for tools that provide real-time monitoring and automated risk assessments, similar to the features offered by Threat Watch. A strong focus on dark web monitoring and phishing detection can also enhance the effectiveness of the chosen solution. Additionally, considering the ease of implementation and the support offered by the vendor can significantly impact the overall user experience and effectiveness of the cybersecurity strategy.
