Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
Pursuit
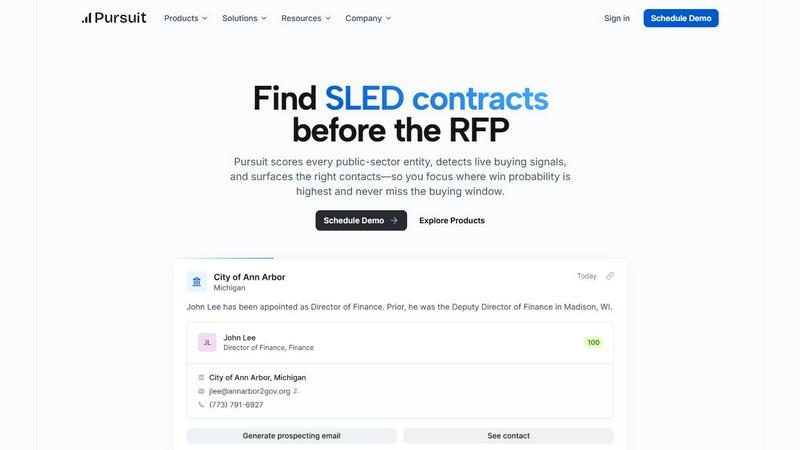
Pursuit is a pre-RFP intelligence platform that helps sales teams win SLED deals by surfacing early buying signals.
Last updated: February 28, 2026
Threat Watch
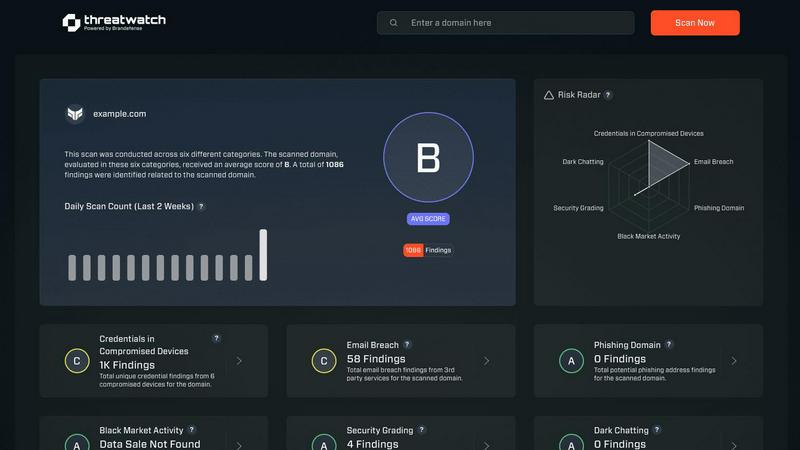
Threat Watch swiftly evaluates your cybersecurity health by identifying vulnerabilities in compromised accounts and.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Buying Signal Detection
Pursuit's proprietary AI engine scans and interprets millions of data points from public records to identify genuine buying intent signals long before a formal procurement process begins. These signals include budget approvals for new initiatives, discussions of pain points in meeting minutes, contract expirations, leadership changes indicating new priorities, and mentions of specific projects or technology needs. This early-warning system is the cornerstone of the platform, transforming sales from a reactive game to a proactive strategic pursuit.
Comprehensive SLED Entity Database & Scoring
The platform maintains a dynamic database of over 110,000 public-sector entities, each profiled and scored based on their procurement activity, budget, technology adoption, and other relevant factors. This scoring mechanism helps organizations instantly prioritize which entities are most likely to buy, enabling efficient allocation of sales resources. Each entity profile includes enriched data on organizational structure, key decision-makers, incumbent vendors, and historical contract awards.
Native CRM & MarTech Integrations
Pursuit is built for operational efficiency with seamless, bi-directional integrations into core go-to-market systems. It natively syncs with Salesforce and HubSpot, ensuring that enriched account data, contact information, and live buying signals flow automatically into a team's existing workflow without manual entry or engineering effort. Marketing teams can also push targeted audiences directly to platforms like LinkedIn Ads, Marketo, and HubSpot for precision ABM campaigns.
Role-Specific Intelligence Delivery
Intelligence is delivered in the format most actionable for each user persona. For BDRs, this means daily prioritized call lists based on fresh signals in their territory. For Account Executives, a Chrome extension provides instant meeting prep with full account intel. Customer Success receives configurable alerts for upcoming renewals and churn risks, while Sales Leaders gain team-wide visibility into signal engagement and territory coverage, enabling better forecasting and management.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch offers a holistic evaluation of an organization's cybersecurity landscape. This feature analyzes critical security categories, providing users with a detailed understanding of their cyber health and highlighting vulnerabilities that need immediate attention.
Real-Time Insights and Alerts
With its real-time monitoring capabilities, Threat Watch continuously scans for potential threats and vulnerabilities. Users receive instant alerts when issues arise, allowing them to respond quickly and effectively to mitigate risks before they escalate.
Dark Web Monitoring
One of the standout features of Threat Watch is its ability to monitor the dark web for compromised credentials and sensitive information. This proactive approach helps organizations stay ahead of potential threats and protects their valuable data from being exploited by malicious actors.
Automated Risk Assessments
Threat Watch automates the process of risk assessment, enabling organizations to quickly identify and prioritize potential vulnerabilities. This efficiency not only saves time but also ensures that security teams can focus their efforts on the most critical issues affecting their cybersecurity posture.
Use Cases
Pursuit
Proactive Pipeline Generation for BDR/SDR Teams
Business Development Representatives use Pursuit to move beyond cold outreach based on firmographics. The platform provides daily, prioritized lists of accounts exhibiting concrete buying signals, such as a school district approving a budget for cybersecurity upgrades or a city council discussing public Wi-Fi initiatives. This allows BDRs to make relevant, timely contact, resulting in significantly higher conversion rates and a more qualified sales pipeline.
Strategic Account Planning for Sales Leaders & AEs
Sales leaders and account executives leverage Pursuit for strategic territory planning and deal execution. The platform reveals the complete procurement landscape for a target entity, including the incumbent vendor, contract value, expiration date, and the specific procurement vehicle likely to be used. This intelligence allows AEs to craft tailored solutions, anticipate competitor moves, and engage with stakeholders from a position of deep knowledge, dramatically improving win rates.
Account-Based Marketing (ABM) Campaign Execution
Marketing teams utilize Pursuit's buying signals to fuel highly targeted and effective ABM programs. Instead of targeting accounts based on static attributes, marketers can build campaigns around real-time events, such as a state agency's new technology initiative or a county's approved budget for infrastructure projects. By syncing these in-market audiences to advertising and email platforms, marketing achieves higher engagement and conversion lifts.
Customer Success & Renewal Risk Management
Customer Success managers employ Pursuit to protect and grow existing revenue. The platform provides configurable alerts 90-180 days before a customer's contract is set to expire, enabling proactive renewal conversations. Furthermore, it monitors for churn risk signals like budget cuts, leadership changes, or competitor RFPs being issued to the client's organization, allowing CSMs to mitigate risk and identify expansion opportunities early.
Threat Watch
IT Security Management
Organizations can leverage Threat Watch to enhance their IT security management processes. By utilizing automated assessments and real-time insights, IT security teams can promptly address vulnerabilities and maintain a robust security posture.
Risk Assessment and Compliance
Risk management teams can utilize Threat Watch to conduct thorough risk assessments that align with regulatory compliance requirements. By efficiently identifying vulnerabilities and exposures, organizations can ensure they meet industry standards and avoid potential penalties.
Incident Response Planning
Threat Watch proves invaluable in incident response planning by providing organizations with critical insights into potential threats. By knowing where their vulnerabilities lie, businesses can develop effective response strategies and minimize the impact of a cyber incident.
Employee Security Training
Organizations can use Threat Watch to identify common phishing addresses and compromised credentials, which can inform employee training programs. By educating staff about these threats, businesses can foster a culture of security awareness and reduce the likelihood of successful attacks.
Overview
About Pursuit
Pursuit is a pre-RFP (Request for Proposal) intelligence platform engineered specifically for businesses selling to the SLED (State, Local, and Education) public sector. It addresses the fundamental challenge of timing and visibility in a market characterized by over 110,000 unique entities, complex procurement rules, and lengthy budget cycles. The platform's core mission is to transform public-sector sales by shifting engagement from reactive RFP responses to proactive, intelligence-driven outreach. By leveraging AI to continuously monitor and analyze a vast array of public data sources—including council meetings, budget documents, board agendas, and contract postings—Pursuit detects live buying signals 6 to 18 months before an RFP is formally issued. This provides sales teams with an unprecedented first-mover advantage, allowing them to shape requirements and establish themselves as the incumbent solution before competitors are even aware of the opportunity. With a comprehensive, continuously enriched database scoring every entity and providing key contact information, Pursuit serves the entire go-to-market organization, from Marketing and Business Development Representatives to Account Executives, Sales Leaders, and Customer Success, ensuring shared intelligence drives cohesive strategy and execution.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform designed to provide organizations with a comprehensive overview of their cyber health. With the increasing prevalence of cyber threats, businesses need a reliable tool that can analyze their critical assets, vulnerabilities, and exposures in real-time. Threat Watch fulfills this need by empowering IT security professionals, risk management teams, and organizational leaders with the insights required to make informed decisions regarding their cybersecurity posture. The main value proposition of Threat Watch lies in its capability to deliver automated assessments and real-time insights, enabling users to swiftly identify, prioritize, and mitigate potential risks. By focusing on essential elements such as compromised credentials, breached accounts, phishing addresses, and dark web content, Threat Watch becomes an indispensable resource in the relentless fight against cyber threats. By integrating this powerful solution, organizations can significantly enhance their security measures, ensure compliance with regulatory standards, and ultimately protect their digital assets from evolving cyber risks.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit detects a wide range of intent signals from public documents and data. Key examples include budget line-item approvals for specific projects, discussions of needs or challenges in council/board meeting minutes, the publication of RFIs (Requests for Information), contract expiration notices, leadership changes that often signal new priorities, and mentions of specific technologies or initiatives in strategic planning documents. The AI contextualizes these data points to confirm genuine procurement intent.
How does Pursuit ensure data accuracy and freshness?
Pursuit maintains a 94% data accuracy rate through a continuous, automated enrichment process. The platform's systems constantly monitor primary source documents from government and educational institutions. Any changes in contacts, organizational charts, budget status, or new procurement activities are detected and updated in the database in real-time, ensuring sales teams are always working with the most current intelligence available.
Can Pursuit integrate with our existing tech stack (CRM, marketing automation)?
Yes, Pursuit is designed for seamless integration. It offers native, bi-directional synchronization with major CRM platforms like Salesforce and HubSpot, automatically pushing enriched account/contact data and buying signals. For marketing teams, it provides direct audience sync capabilities with LinkedIn Campaign Manager, Marketo, and HubSpot, enabling signal-based campaigns without manual data export or import processes.
Who within my organization is Pursuit designed for?
Pursuit is a platform built for the entire go-to-market team selling to SLED. This includes Revenue Operations for data management, Sales Leaders for forecasting and coaching, Marketing for ABM, Account Executives for deal execution, Business Development Reps for outbound prospecting, and Customer Success for renewal and expansion management. Each persona receives tailored insights and workflows within the same shared intelligence platform.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes across various industries. It is particularly beneficial for IT security professionals, risk management teams, and organizational leaders who require comprehensive cybersecurity insights.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to continuously scan the dark web for compromised credentials and sensitive information related to its users. This proactive monitoring helps organizations stay informed about potential threats.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security tools and systems within an organization. By integrating seamlessly, it enhances the overall cybersecurity framework, providing users with a more comprehensive view of their cyber health.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to evaluate its capabilities. This allows potential users to experience the platform's features and benefits before making a commitment.
Alternatives
Pursuit Alternatives
Pursuit is an AI-driven business intelligence platform designed to streamline public sector sales. It specializes in scoring government and educational entities, detecting live buying signals, and identifying key contacts to help businesses win more contracts. This places it within the competitive landscape of sales intelligence and government procurement software. Users may explore alternatives to Pursuit for various reasons, including budget constraints, specific feature requirements not covered by the platform, or a need for a tool that integrates with a different technology stack. Some organizations might seek a broader market intelligence solution or one with a stronger focus on a different vertical beyond the public sector. When evaluating alternatives, key considerations should include the depth and accuracy of the entity database, the sophistication of buying signal detection, CRM integration capabilities, and the platform's specialization in public sector procurement processes. The quality of contact data and the real-time nature of opportunity alerts are also critical factors for sales teams targeting government contracts.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity intelligence tool designed to help organizations evaluate their cyber health comprehensively. It falls under the category of business intelligence, specifically focused on cybersecurity. Businesses often seek alternatives to Threat Watch for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. As organizations evaluate their options, it’s essential to consider factors such as the level of automation, the comprehensiveness of threat coverage, integration capabilities, and user-friendliness of the alternative solutions. When choosing an alternative to Threat Watch, users should look for tools that provide real-time monitoring and automated risk assessments, similar to the features offered by Threat Watch. A strong focus on dark web monitoring and phishing detection can also enhance the effectiveness of the chosen solution. Additionally, considering the ease of implementation and the support offered by the vendor can significantly impact the overall user experience and effectiveness of the cybersecurity strategy.
